By Chris Honda, Director of Security, Risk & Compliance, Whistic
I run the compliance program here at Whistic, and we just finished an ISO surveillance audit. I've spent the last several years working in security and risk, most of it here at Whistic, building our internal program, sitting through audits, and working alongside customers as they navigate theirs. So when our team started building our new agentic Compliance application, I had a front-row seat as both an internal sounding board and a daily user.
This post is a chance to share what we built, why we built it, and where we're taking it over the next several months.
The thesis, in one line: passing an audit and reducing risk are not the same thing. They never were. The industry just got comfortable pretending they were. That's ending, and Whistic Compliance is built for what comes next.
The industry has a compliance problem it won't say out loud
Walk the floor at any security conference this year and you'll hear the same pitch from a dozen booths: “We'll get you SOC 2 ready faster. Connect your stack, auto-collect evidence, generate the reports, pass the audit.”
That's a fine pitch. It also has very little to do with whether your security program is actually working.
You know the platforms I'm talking about. Most of you have probably used one of them. Some of them are good at what they do: quickly producing the artifacts an auditor needs, mapping connected systems to a framework, generating clean reports. None of that is wrong. But it's a narrow definition of compliance, and the market has started to notice.
A high-profile incident at one of these compliance automation platforms, alleged fraud at a startup whose certifications a lot of customers had been treating as a stamp of trust, has touched off what I'd call a reckoning. I don't think it's done. I think we're in the early innings of a market correction, and the ripples will last for years.
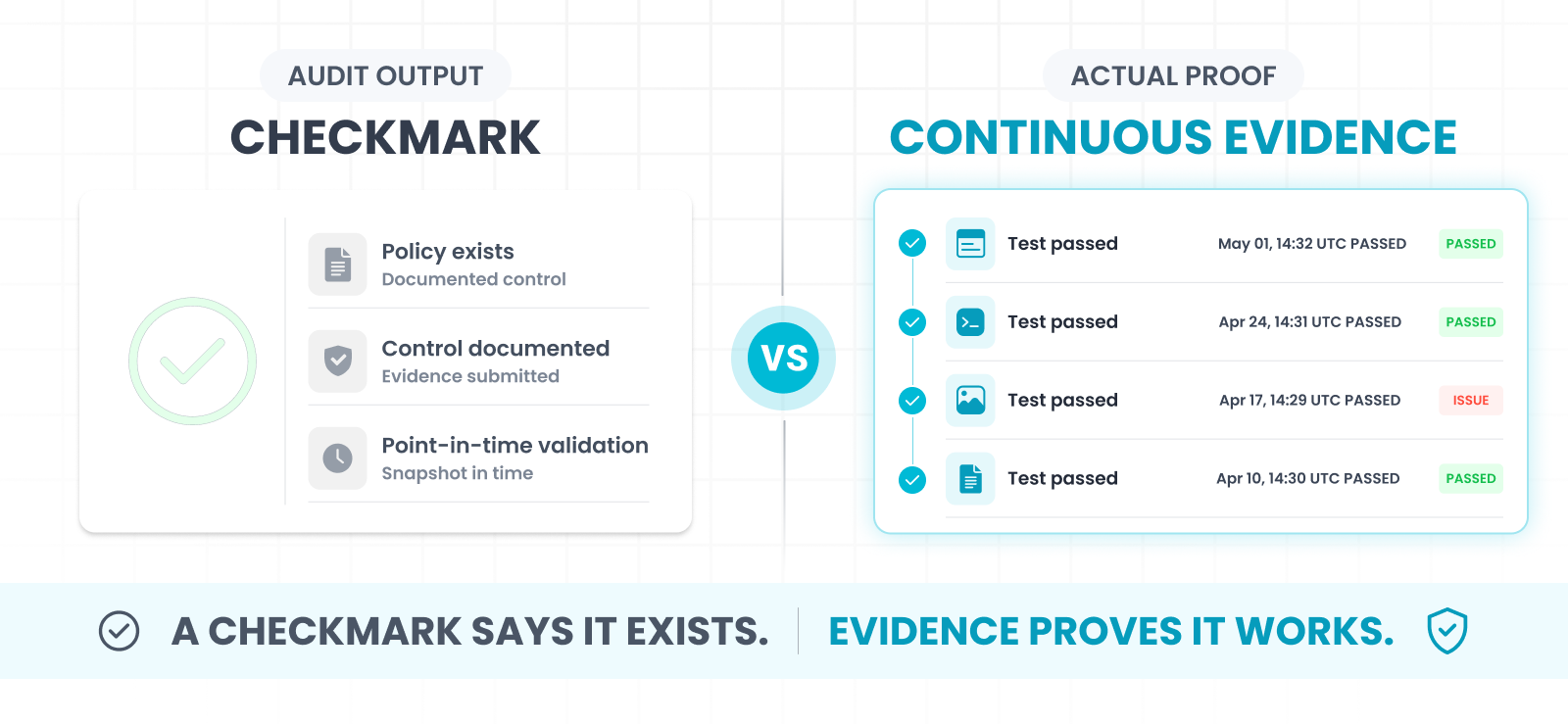
The correction itself is simple. Documentation isn't proof. A green checkmark isn't evidence. The tools that made compliance feel easy by lowering the bar are about to feel less safe than they did six months ago.
That's the world Whistic Compliance is built for.
What we shipped
Whistic Compliance is a new arrival on the Whistic platform, joining Trust Center, Whistic Assess, and Vendor Monitoring. It lets security and compliance teams do four things in one place:
- Define controls. Plain-English description of a policy or requirement your team enforces. “All production databases must be encrypted at rest.” Title and summary defined in unambiguous terms.
- Write tests against those controls. Manual evidence upload or AI-powered Browser Agent validation on a scheduled cadence.
- Capture evidence automatically. Every test execution creates a permanent, timestamped record with screenshots, results, and AI notes.
- Build an audit trail that lives. Six months of weekly tests proving your S3 buckets stayed encrypted, instead of a single green checkmark on a dashboard.
The piece I'm most excited about is the Browser Agent. You give it a target system, natural-language instructions (“go to the AWS console, navigate to S3 bucket settings, screenshot the default encryption config”), and pass criteria. The AI navigates. It captures. A human reviews and makes the final call.
That last part is intentional. We built this AI-first, but not human-out. Karl Ford, our VP of Engineering & Product, framed it well during one of our internal reviews:
“The agent is great at the navigation work that takes a person twenty minutes and produces nothing memorable. The decisions worth making are still decisions. The product needs to know the difference.”
That's the design philosophy. Offload what can be automated so the practitioner spends their attention on what actually requires judgment.
The difference, in one example
A typical compliance automation tool will tell your auditor: “You have a data protection policy. ✅ Green checkmark.”
Whistic Compliance gives your auditor something else:
Here are six months of weekly tests showing all our buckets, all our databases, encrypted. Screenshots showing we've had this enforced the whole time. Not a green checkmark that says we do data protection: the actual exported configuration, the timestamped screenshot, the agent log.
That's the difference between documentation and proof. Between a control that exists and a control that works.

I want to be precise about what we're claiming. Whistic doesn't reduce your risk for you. We don't make security decisions on your behalf or tell you what’s most important. We make it possible for you to know, and prove, what's actually happening in your program. That's the job. The decisions belong to you.
Why compliance sits next to TPRM
This is the part of the platform we built deliberately, because we saw the pattern in our customer feedback before we shipped a line of code.
Whistic customers already use the platform to do two things on opposite sides of the same problem:
- Verify their vendors through Whistic Assess and Vendor Monitoring, demanding real evidence from suppliers, not just questionnaire answers.
- Share their own security posture with customers through their Trust Center, telling their own trust story externally.
Compliance closes the loop. The same vendor that demands real evidence from its suppliers can finally produce real evidence for its own auditors and customers. Internal compliance now does for your own controls what Whistic has always done for external trust: replace static documentation with continuous, evidence-backed proof.
One platform. One timeline. One AI architecture.
There's a flywheel here. If you're running a strong TPRM program, you've already developed the operational muscle compliance needs: clear ownership, recurring cadence, evidence discipline. If you're running a strong compliance program, you've already developed the rigor a serious TPRM program runs on. They reinforce each other, but only if they live in the same system. Many companies run them in two systems with different data models, different review cycles, and different teams. We don't think that's the future shape of risk operations. We think the future is one connected program, agentic from end to end. That's what we're building.
Where Whistic Compliance is going
The current release is a strong foundation. You can define your controls, write tests, run those tests with the Browser Agent or manually, capture timestamped evidence, and build the kind of audit trail most teams don't have today.
Here's the order we're building in over the next several months. Some of these capabilities are clustered into the same release window; some come in waves. I'm not going to put exact dates on them because the timing depends on customer feedback. But this is the direction.
Coming next: Deeper verification and external sharing
Deeper automated verification. Beyond the Browser Agent, we're adding command-line and API-driven test types for technical teams that want to verify infrastructure directly: pull a config from AWS, check an MFA setting in Okta, run an automated query against your environment. Same evidence trail, deeper verification.
LLM-interpreted results. AI doesn't just run the test. It interprets what it sees, flags drift, and surfaces anomalies before they show up in an audit.
External evidence sharing with assessors. Today, when an auditor asks for proof, you point them to a SOC 2 report. In the next wave, you point them to six months of timestamped tests showing the control actually held. The path forward is showing your work, not pointing to a certification. It's harder to fake, and it's a lot more useful.
This is where compliance evidence stops being something you scramble to produce for your auditors and customers, and starts being something you publish to them, continuously, with the same rigor your Trust Center already brings to your security posture.
After that: Framework mapping and program visibility
Framework auto-mapping. Hand Whistic your last SOC 2 report or ISO 27001 surveillance, and the system understands your existing requirements, translates them into controls, and recommends the tests to verify them. No more rebuilding your program from scratch every time you adopt a new framework.
Cross-framework intelligence. The same control that proves encryption-at-rest for SOC 2 maps cleanly to ISO 27001, HIPAA, and the controls your largest customer's questionnaire is asking about. One test, many requirements satisfied.
Program-level visibility. A leadership view that actually means something. Not a vanity dashboard. Real visibility into which controls are holding, which need attention, and where risk is creeping up.
The bigger vision: GRC that actually reduces risk
Today, GRC and security operate as separate disciplines that occasionally talk to each other. I think that's the wrong shape. Five years from now, the GRC function should look a lot more like good security engineering: embedded in product, engineering, and operations as a proactive discipline, not a reactive checkpoint that slows things down. Define your controls in the platform that runs your TPRM. Test them with the same AI architecture that powers your vendor assessments. Share the proof through the same Trust Center your customers already trust. Let the agents do the manual work. Let your team make the decisions that need a human.
That's the world Whistic is building toward, and Compliance is the next major piece of it.
On AI: Where we're pushing, and where we're holding
Whistic is aggressively AI-first. Every application — Assess, Trust Center, Vendor Monitoring, Compliance — is built on the same agentic AI architecture, and we're not waiting for the implications to be fully proved out before we ship. Juan Rodriguez, our CEO, has been clear about why:
“Software used to give you a tool, and you did the work. The shift now is to software that does the work with you: agents handling the heavy lifting, humans making the calls that matter. The whole industry is going this direction. We're going to get there first, and we're going to get there from a position of strength.”
But there's a line we won't cross. AI making the final call on risk decisions is a place we are deliberately not going. The Browser Agent navigates and captures. A person reviews and decides. The agent flags drift. A person decides what to do about it. We're going to keep extending what AI can verify, interpret, and surface. We're not going to put AI in the seat where the buck stops.
That's a deliberate choice. It's the one our customers keep telling us they want.
What This Means If You're a Whistic Customer
A few specifics, by team shape:
- If you're already running TPRM in Whistic and you've been managing internal controls in spreadsheets, Compliance is the natural next step. It lives in the same platform, uses the same AI, and connects to the Trust Center you're already publishing to.
- If you're preparing for SOC 2 or ISO 27001, Compliance gives you the evidence trail those audits actually require: not just documentation that the controls exist, but timestamped proof that they've been working.
- If you're managing 20+ controls manually and feeling the audit-cycle scramble, this is the inflection point.
- If you've been evaluating other compliance automation platforms, the question to ask isn't which tool checks more boxes faster. It's which tool actually proves the boxes are real.
Try Whistic Compliance and compare. Look at how deep the evidence goes. The audits ahead are going to be scrutinized differently than the audits behind us, and the evidence you bring needs to hold up.
The market is moving toward a place where saying you're secure isn't enough. You're going to have to show it. Continuously. With evidence. To your auditors, to your customers, to your board. The tools that win the next five years will be the ones that make that easy, not the ones that make passing the audit easy.
Book a demo. Try it. Compare the depth of the evidence. Then tell us what to build next. We're listening.
— Chris Honda
Director of Security, Risk & Compliance, Whistic
FAQs
What is Whistic Compliance?
A new application on the Whistic platform that lets security and compliance teams define internal security controls, run tests to verify those controls are working, and capture timestamped evidence on a recurring schedule. It launched on May 7, 2026, and is one of four applications in the Whistic platform alongside Trust Center, Whistic Assess, and Vendor Monitoring.
How is this different from other compliance automation tools?
Most compliance automation tools optimize for passing audits: connect your systems, auto-collect evidence, map to a framework, present a report. Whistic Compliance is built around proving a control is actually working, not just documenting that it exists. The difference shows up in the evidence: instead of a green checkmark, you get timestamped tests, screenshots, and results that demonstrate continuous enforcement. We also sit alongside a purpose-built TPRM platform, which most compliance tools do not.
What is the Browser Agent?
An AI agent that navigates to a target system, follows natural-language instructions, and captures screenshots as evidence. You define what the test should do and what passing looks like. The agent does the navigation; a human reviews the result. The Browser Agent is best-effort, currently targeting an 80%+ success rate, and is not positioned as fully autonomous.
Does it support CLI or API-based automated tests?
Not in the current release. CLI and API-driven automated tests are part of the next wave of capabilities on our roadmap. Today's release supports manual evidence upload, Browser Agent verification, and scheduled recurring runs.
Does it auto-map to SOC 2, ISO 27001, or HIPAA?
Not yet. Framework auto-mapping is on the roadmap as part of a later wave of capabilities. The current release is framework-agnostic. Define the controls your program needs and run tests against them. Customers preparing for any framework can use Whistic Compliance now, but the mapping work is manual at launch.
Can I share compliance evidence directly with my auditors or customers?
Not in the current release. External evidence sharing, internal control evidence flowing into your Trust Center for assessors and customers, is part of the next wave of capabilities. Today, the evidence trail is internal.
Is the Browser Agent reliable enough to trust?
Best-effort. The AI does the navigation and capture. A human always reviews and makes the final pass/fail call. The reliability of any given test improves the more specific your instructions and pass criteria are. We do not position the Browser Agent as autonomous, and we do not claim it never makes mistakes.
Who is Whistic Compliance built for?
Security and compliance teams managing controls today through spreadsheets, shared drives, or point-in-time audits. Teams preparing for or maintaining SOC 2, ISO 27001, or HIPAA. Organizations managing 20+ controls where re-verification every audit cycle is becoming unsustainable. Existing Whistic customers who want to close the loop between the trust they share externally and the controls they enforce internally.
How does it connect to Whistic's TPRM and Vendor Monitoring?
Same platform, same AI architecture, same data model. The same team running TPRM in Whistic can manage internal controls in Whistic. Compliance, TPRM, Vendor Monitoring, and Trust Center are designed to work as one connected risk operations platform, not four bolted-together products.
Is Compliance available standalone or only with TPRM?
Both. Existing Whistic customers can add it as a paid add-on. Net-new buyers can purchase it standalone.
Where can I see it in person?
Juan Rodriguez, our CEO, is speaking at ISACA Conference North America on Wednesday, May 6 at 9:50 a.m. PT on the Innovation Stage: Beyond Assessments: The New Standard for Agentic TPRM, Vendor Monitoring & the Future of Compliance. Whistic is exhibiting at ISACA Booth 303 (May 6–8), demoing Compliance at a public webinar on May 14, and on-site at the Gartner Security & Risk Management Summit in National Harbor, MD (June 1–3).