Join a community of peers like Okta, Airbnb, Zendesk, Atlassian, Snap, and G2 in the Security First Initiative

Members work together via in-person and virtual meetings to network and learn from cybersecurity experts and tackle the industry’s biggest challenges.

Members can participate in PR campaigns, contribute articles, and speak at events on behalf of the Security First Initiative.

Whistic provides support to members to ensure they can easily add their vendor community to the Whistic Network—free with a Basic Whistic Profile.
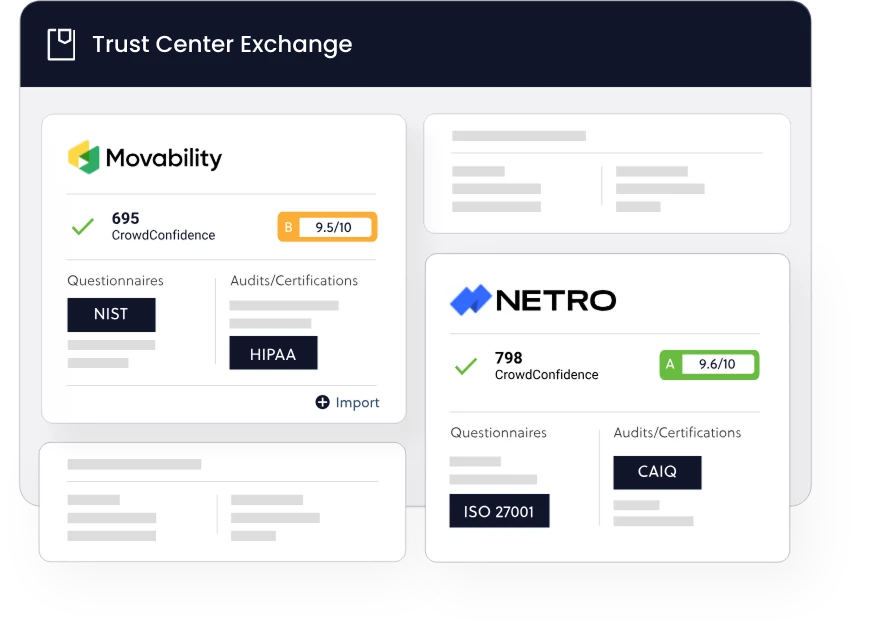
The Whistic Vendor Security Network
Our network of software buyers and sellers is transforming third-party risk management without the need to request or respond to questionnaires. The Whistic Trust Center Exchange is a dynamic, robust exchange for on-demand security information.

Our Whistic Profile
Transparency builds trust. Zero-Touch Assessments are possible when software buyers and sellers share security information proactively. We practice what we preach, so our security information is publicly available in our Whistic Security Profile.
Our commitment to total transparency regarding the data we collect from you and those you invite into the Whistic Network
Purposeful collection that is never sold
We only collect data that has a purpose. We regularly review our processes to ensure we never over-collect. And we’ll never sell your data. It’s as simple as that.
Respect for your control of data access
Data sharing is fundamental to the success of the Whistic Network, so we believe in giving you the ability to control how and to whom your data is shared.
Privacy Policy and Terms of Service
To learn more about our approach to privacy and our commitment to protecting your personal data, please read our complete Privacy Policy. To learn more about how you control the sharing of your customer data, please read our full Terms of Service.
One AI-driven Platform. 360 TPRM. Getting started is easy.
Explore Whistic your way—watch a demo, dive into resources, or jump right in with your own security Profile.
Certifications and Security Partnerships








