Streamlined Assessments for Everyone
The Whistic Network powers trusted relationships between vendors and their customers. Connect with thousands of companies, enable security transparency, and eliminate the tedious, time-consuming assessment process.

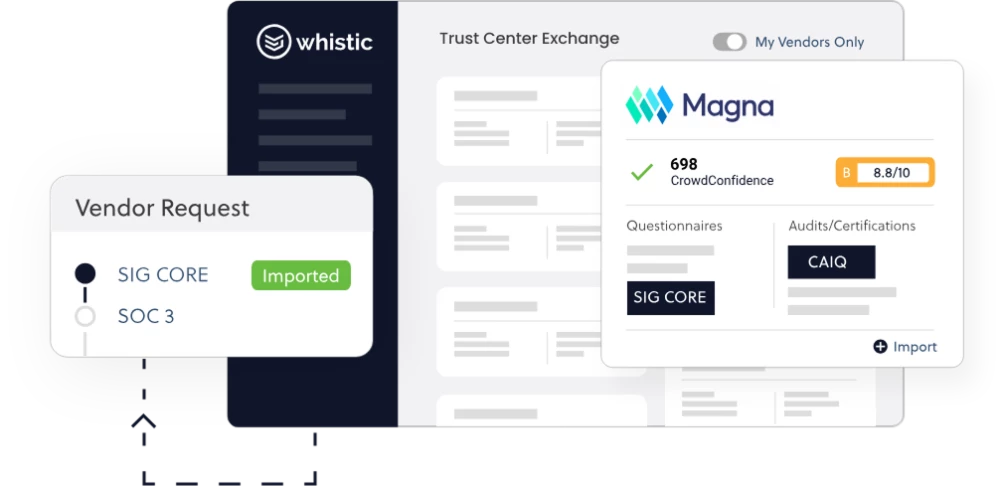
On-Demand Security Postures
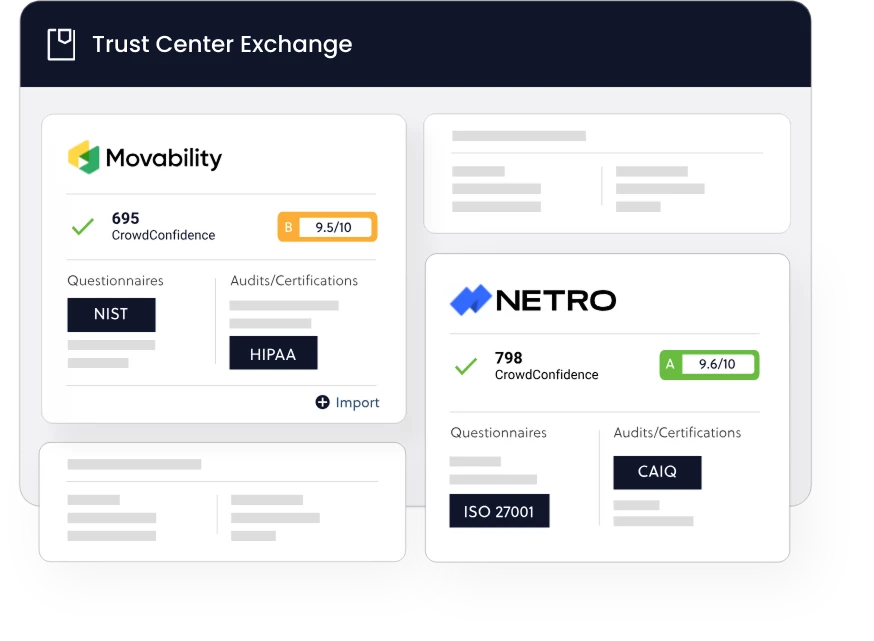
Significantly reduce the time it takes to identify and evaluate new vendors: quickly find and view security documentation, compliance information, questionnaires, certifications, and audits for thousands of companies.
Connect with Your Buyers
Make it easy for hundreds of top companies to buy from you! Publish your security posture in the Whistic Trust Center Exchange to enable frictionless Zero-Touch Assessments and eliminate questionnaire requests.
Whistic Trust Center Exchange Connects You to the World’s Most Dynamic Network of Vendors and Customers in Seconds
Evaluate the security posture of thousands of companies in Trust Center Exchange—including continuous monitoring of the top 50 by RiskRecon—for a complete, 360-degree view of vendor risk.

Google, Microsoft, Zoom, and thousands more rely on Whistic Trust Center Exchange to efficiently meet their customers’ vendor risk-management and compliance needs.

Supercharge automation to eliminate time-consuming tasks, identify insights, and share information fast.

Share only what you want to share with approval workflows, audit trails, and NDA safeguards.

Use reports to measure and act on customer engagement, and optimize your security posture to grow your business.

Trusted by the world’s largest network of buyers and sellers




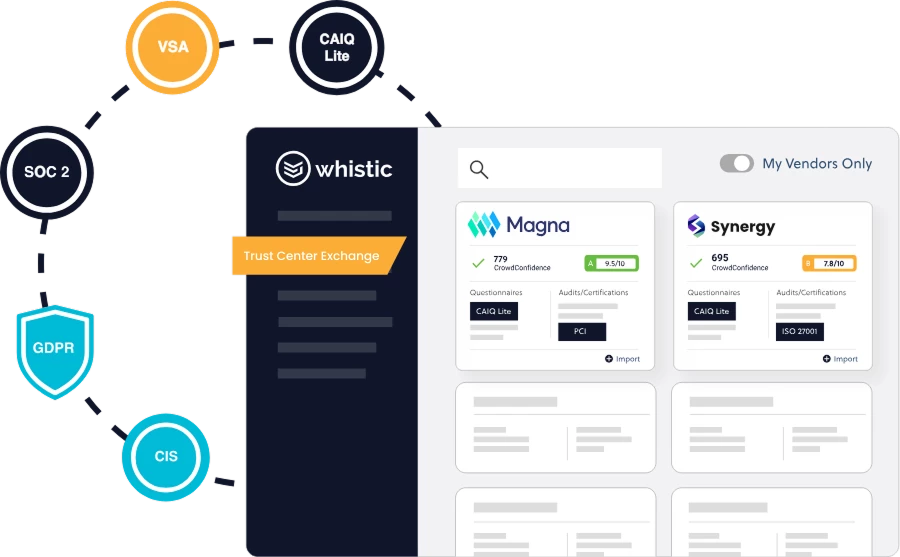
Access 40+ Questionnaires and Frameworks
Find and view vendor Profiles aligned to the latest versions of more than 40 questionnaires and frameworks, including rapid-response templates for industry-wide vulnerabilities, and leverage continuous monitoring by RiskRecon on over 50k companies.
Trusted by thousands of people and companies
The Ultimate Guide to Vendor Risk Assessment
This in-depth guide is full of all the steps, tips, and insights you’ll need to modernize your approach to third-party risk management.
Download the Guide

Whistic helps a Financial Services Company eliminate spreadsheets and streamline assessments

Whistic the Complete Vendor Security Platform

SingleStore builds and matures its vendor security program with Whistic
One AI-driven Platform. 360 TPRM. Getting started is easy.
Explore Whistic your way—watch a demo, dive into resources, or jump right in with your own security Profile.
Certifications and Security Partnerships













