Introducing Vendor Monitoring: continuous breach and hack detection, built into the platform where your vendor risk work already happens.
There's a question we started asking security and risk teams over the past several months. It's a simple one, and the answers were striking.
"If one of your critical vendors had a breach today — right now — how would you find out?"
The most common answers: a news headline. An email from the vendor, maybe. A customer complaint. Someone on the team spotting something on LinkedIn.
When we pushed further — "how confident are you that you'd know within 24 hours?" — teams rated themselves a 5 out of 10.

This is not a niche problem. It's not a problem that affects only the smallest teams or the least mature programs. We heard it from financial services firms managing hundreds of vendors. From healthcare organizations with strict regulatory obligations. From fast-growing SaaS companies with lean security teams and expanding vendor portfolios. Across customer conversations, the story was remarkably consistent: annual assessments are strong. The eleven months in between are a blind spot.
Today, we're closing it.
The Gap No One Talks About
Most TPRM programs are built around a single moment in time. You assess a vendor. You document the findings. You mark it complete and schedule the next review in twelve months. The program looks thorough on paper.
But risk doesn't run on your assessment calendar. Breaches happen in month four. Ransomware groups don't check your renewal dates. A vendor's SOC 2 certification says nothing about what happened last Tuesday.
The teams we talked to knew this. Across call after call, we heard variations of the same frustration. Teams were relying on Google Alerts. Manual inbox scanning. Hoping vendors would self-report. One team described their approach as "hearing it from the vendor, if they bother to tell us."
The problem isn't that security teams don't care. It's that the tools available forced a choice: add another dashboard to check, pay $25K to $100K or more for an enterprise-grade monitoring platform, or accept the blind spot and move on.
We think that's the wrong set of options.
Monitoring That Actually Does Something
Vendor Monitoring is built on a straightforward belief: knowing about a risk isn't the same as doing something about it.
Most monitoring tools stop at the alert. They surface a signal, send a notification, and hand the problem back to you, disconnected from any context, any history, any clear path to action. The result is either alert fatigue (too many notifications with too little signal) or a fire drill every time something real comes through.
Whistic Vendor Monitoring works differently. It's not a separate tool. It's not another dashboard to log into. Breach alerts live inside vendor profiles, right alongside assessment history, compliance documents, and risk data, because that's where the work already happens.
When a breach or hack is detected, you get a structured alert: severity rating (Critical, High, Medium, or Low), cause, scope, actors, and ongoing status. Evidence is included, with source links for public disclosures and screenshots for dark web sources. From that single alert, you can do three things that matter:
-
Update the status to track your team's response from discovery to resolution
-
Create an Issue to coordinate internally or go directly to the vendor
-
Start an Assessment, a targeted ad hoc review of the affected vendor, launched in one click
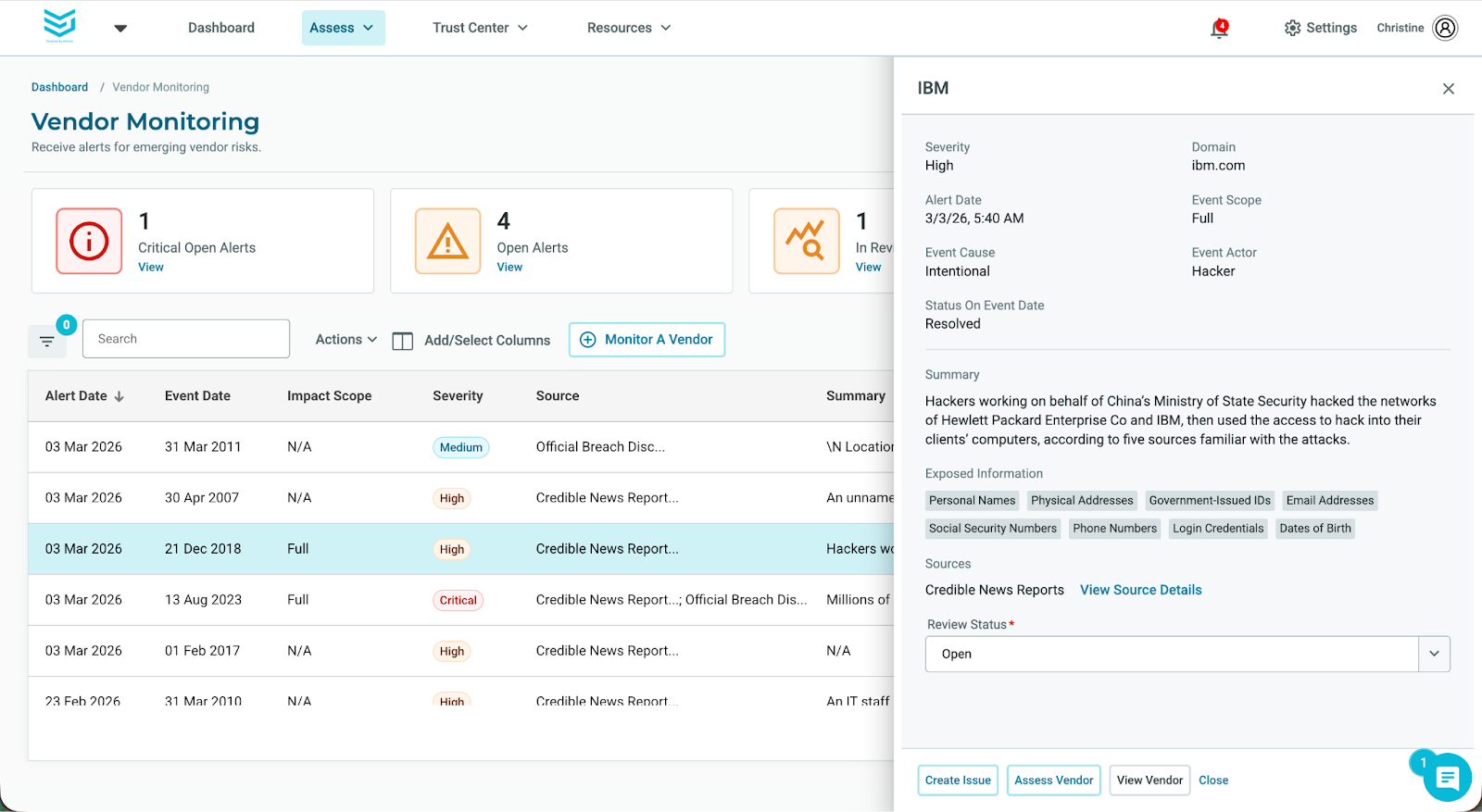
No tool switching. No copy-paste into a ticket. No trying to remember which platform has the vendor's assessment history. One platform, one workflow, one audit trail.
"Continuous monitoring is a must-have for our program. I want it integrated into Whistic rather than using multiple software solutions. That's what my leadership expects."
Sr. InfoSec and GRC Analyst at a LegalTech company
Two Types of Teams. One Problem.
In our customer conversations, a clear split emerged in how teams experience the monitoring gap, and it's worth naming directly, because the same product solves two different problems.
The first group are small teams, often one or two people, managing a hundred or more vendors. All their bandwidth goes to assessments and renewals. Monitoring is an afterthought, not because they don't care, but because there's been no affordable, practical way to do it inside their existing workflow. For these teams, Vendor Monitoring is foundational. It's the first time they'll have real visibility into whether their vendors have been compromised between assessment cycles.
The second group has mature TPRM programs that technically have monitoring tools but are drowning in alerts that don't connect to action. Alert fatigue is real. When something important comes through, there's no clear path to response. The tools live in a separate system from the assessment workflow, which means triage involves email threads, spreadsheets, and manual effort at exactly the moment when speed matters most. Their current tools tell them something happened. Whistic makes sure something gets done about it.
What Continuous Actually Means
A word on how this works, because "continuous monitoring" gets used loosely.
Vendor Monitoring scans vendor domains for breach-related activity, including public sources, news, official disclosures, and dark web signals, with updates processed every 30 minutes. This is not a security score. It is not a risk rating. It does not replace RiskRecon or BitSight for organizations that rely on posture scoring. What it does is fill the operational gap those tools leave: the space between "something happened" and "we did something about it."
Monitoring is enabled per vendor, which means you can prioritize the vendors that actually matter rather than getting too many alerts that don’t matter, or for that matter paying for indiscriminate coverage across your entire list. Allocations can be reassigned at any time, and alert history is preserved even when monitoring is disabled.
For dark web alerts, where direct links can't be surfaced, evidence is provided as a screenshot with context, so teams can make a risk decision without navigating to sources they shouldn't be near.
The Audit Question Everyone Gets Wrong
Here's a question that comes up in compliance reviews, board meetings, and post-incident analysis more often than most security teams want to admit:
"You found out about the breach. What did you do, and when did you do it?"
Most teams can't answer that cleanly. Because most teams handled it in email. Or a spreadsheet. Or a Slack thread that nobody archived.
Vendor Monitoring creates the closed-loop record that answers this question. Every alert, every status update, every issue created, every assessment launched: all of it lives in Whistic, timestamped and traceable. When leadership asks, when auditors ask, when regulators ask, the answer is ready.
See It in Action
Walk through Vendor Monitoring in either our interactive product demo or video demo below and see how an alert becomes an action in a single workflow.
👉 Watch Short Video Demo